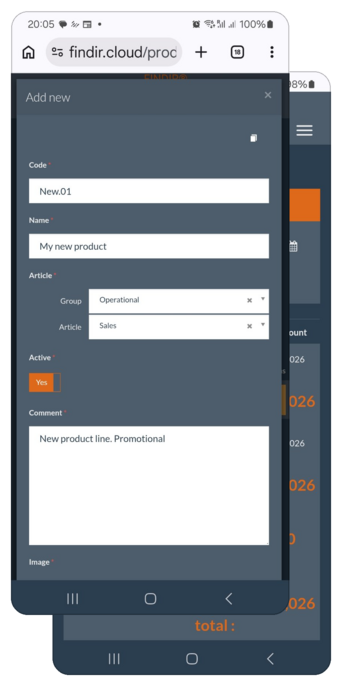
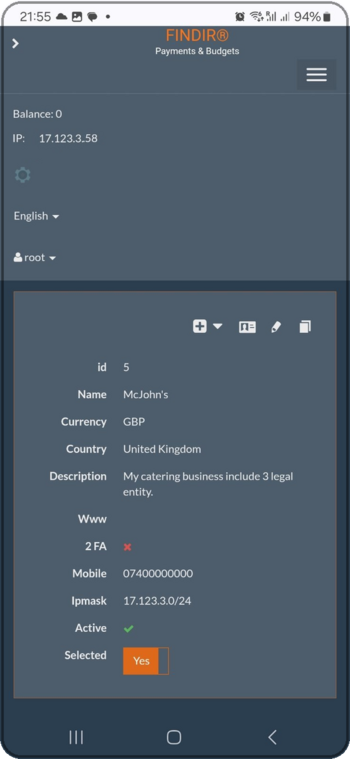
Let your business grow super fast and secure, with FINDIR.
If your current software forces your team to work its way, We can build together your lifestyle workflow: an accounting system that can be tailored around your established processes — from workflow and approvals to reports, client onboarding, integrations, and even your branding. You keep your traditions and working style; the system adapts to you.